Cracked apps? - Here is why you should never use them
How does the crack work?
A crack file is a patch file or a part of the program which has been reverse engineered to bypass the protection or unlock the limitations set by the makers so it can be used without requiring the license keys or authorization from the makers.
The risks of using the cracked software?
Put aside the morality of stealing intellectual properties, here are some risks you are taking:
- You are installing malware. Hackers might inject some malicious code into the cracked app and it will slow your computer down, send out your sensitive information, damage your files…
- It might stop working when you need it the most. The developers often run the registration check and find out the unauthorized uses, the access will be terminated.
- You ain’t got no support. It’s important that you are running the most up-to-date version of the database software with all database security patches installed to remove known vulnerabilities Without the appropriate license, you you can not update, and you don’t have anyone to turn to if something bad happens.
- You could be sued. Downloading and running copyrighted software when you don’t have a license to do so is copyright infringement and thus is illegal.
- It puts hardworking people out of work. Remember that selling license and charging for usage is a way to support the development of the apps. Without enough money, there will be no incentive to continue the work. No work, no app.
Using a cracked software is like exchanging your house key for a gift from an unknown person who is totally fine with breaking the law.
Should you trust them?
And for database security…
For a business, if the production database containing business data is not the most important assets, then I don’t know what else it can be. And using cracked software is one easy way to lose it.
Let’s take an example when someone decided to use a cracked BI tool instead of purchasing a license. The cracked application might copy the database credentials and send them out secretly. Hackers then will have full control of the root access. SSL might prevent them from sniffing packet from the connection but in this case, it adds no difference. It’s gonna be a huge loss.
Who is willing to do such a trade off like that?
How about the free and open source software?
This seems to be a very good alternative. The pros and cons of using open source software have been discussed in this post. It’s up to your needs and requirements.
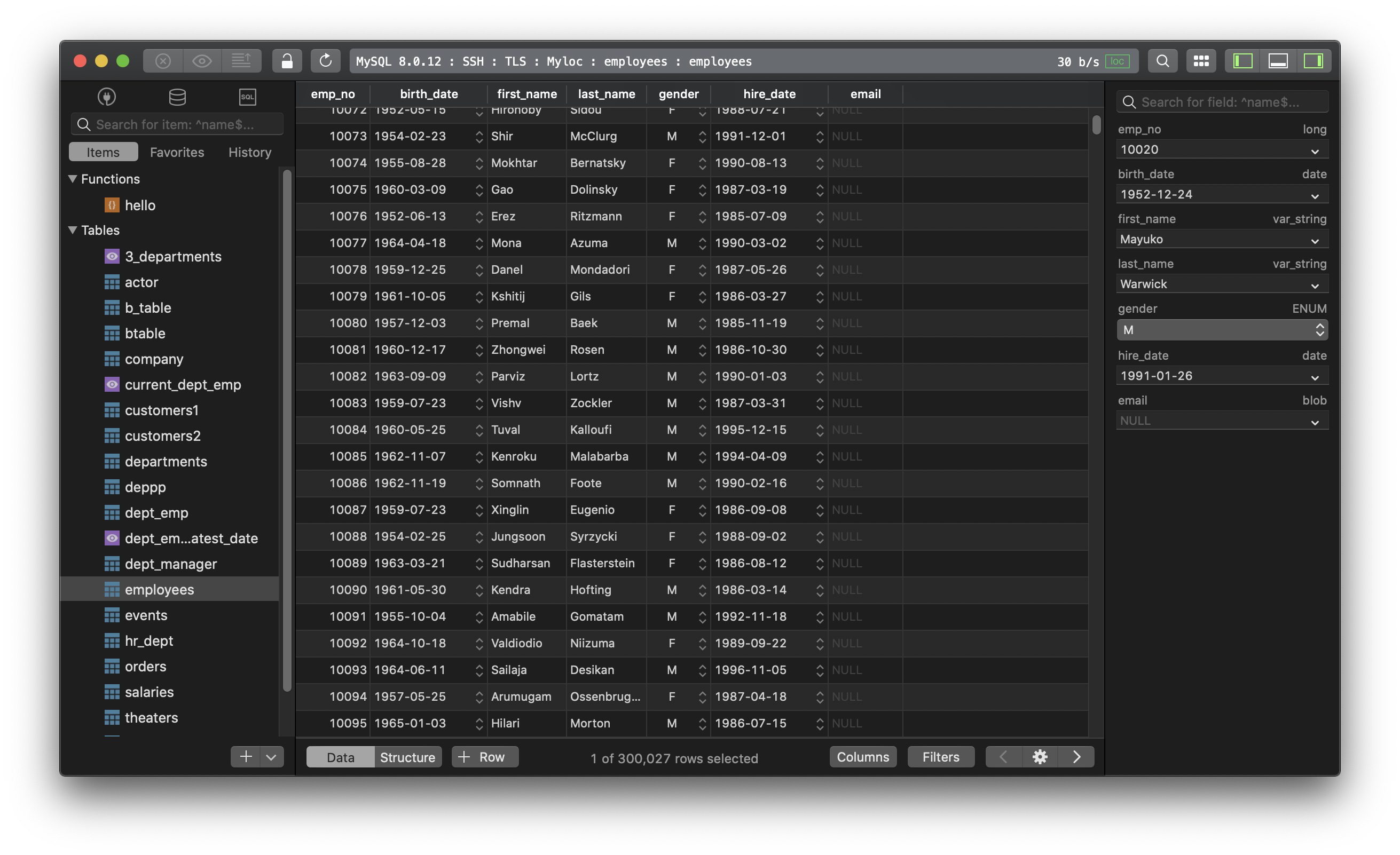
TablePlus is a modern, native tool with an elegant UI that allows you to simultaneously manage multiple databases such as MySQL, PostgreSQL, SQLite, Microsoft SQL Server and more.
Not on Mac? Download TablePlus for Windows.
On Linux? Download TablePlus for Linux
Need a quick edit on the go? Download TablePlus for iOS.